Surprise! You Included a Static Link to a Vulnerable Library
A new NetRise report shows how unexpected vulnerable components are included in the build process, making source-code derived SBOMs obsolete.
Static
Linking
Libraries linked at compile time can hide vulnerable versions your scanners never see.
Build Time
Dependency
Resolution
Build tools can silently pull in outdated components that never appear in your SBOM.
Vendored Dependencies
Third-party vendors often bundle hidden code that isn’t declared in manifests but still ships in your software.
Transitive
Dependencies
Dependency chains can introduce legacy modules that slip past scanners and manifest-based SBOMs.
Appsec Testing and Vulnerability Management
Scanners Stop at Source Code
SBOMs and scans often miss components added during build or bundling, creating a false sense of security that hides vulnerabilities in what’s really shipped.
For Product Security Leaders
Validate your SBOMs and reduce downstream risk before release.
For Third Party Risk Managers
Challenge vendor SBOMs and self-attestation and protect your org with binary analysis.
For CISOs & Executives
Report to leadership with confidence that you’ve reduced risk to your business.
Learn How to End the False Sense of Security That SBOMs From Source Code Provide
FREE REPORT - NO FORM FILL
Why Traditional SBOMs and Scanners Miss What’s Really Inside ...
- OpenSSL 3.0.0 was found inside Python during build — invisible to AST scanners.
- Vendored dependencies like zlib 1.2.8 in rsync evade detection too.
- Misconfigurations, hard-coded secrets, and legacy cryptography often persist unless you validate binaries.
The bottom line: you don’t really know what you’re shipping, or buying, until you enrich your SBOMs with binary analysis.


Verify, Then Trust
SBOMs derived from source code miss vulnerabilities and non-CVE risk. Build comprehensive, accurate SBOMs by analyzing compiled code.
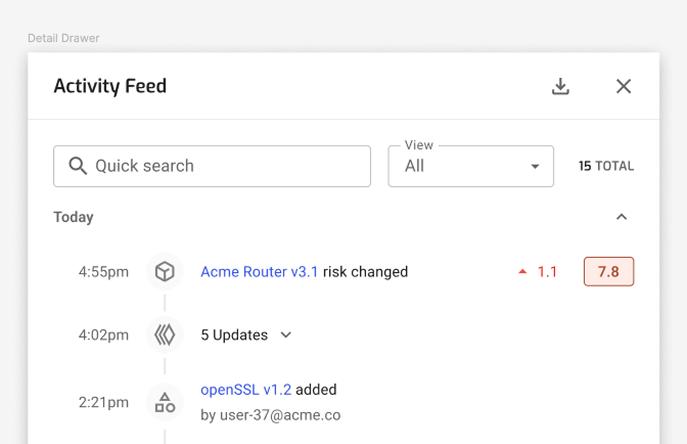
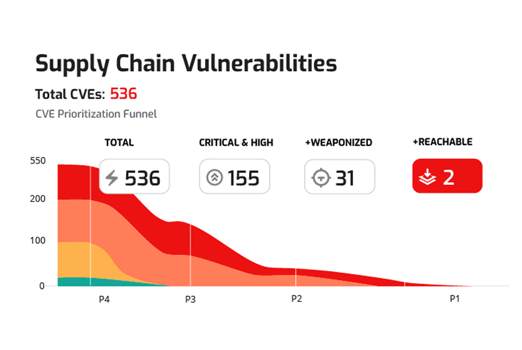
Enriched Vulnerability Context & Prioritization
Not all vulnerabilities imply risk. We map findings to execution paths, startup modules, and network exposure so you fix what attackers can reach.
.png?width=687&height=444&name=Rectangle%20161125835%20(1).png)
Evidence-Backed SBOM for Compliance
Generate SBOMs validated by binary analysis that stand up in audits and regulatory reviews.

Request A Personalized Demo
If your SBOM doesn’t reflect compiled reality, you’ve got blind spots. See how NetRise turns it into a defensible, evidence-backed inventory, and closes the gaps scanners leave behind.
.png?width=112&height=112&name=image%207%20(5).png)




