The Ghost in the Machine
In the world of XIoT security, we have learned some unfortunate and difficult lessons over the past decade. Events like Mirai, Shellshock, Heartbleed and Log4J have left so many of us with the question … “What’s next? And will it affect me?” Just as importantly, “will it be more or less destructive than what has come before?”
The reality we are facing now is that 2021 was a year of significant growth of incidents within XIoT (IoT, OT, and ICS) Security. We had attacks like Kasaya, JBS, Colonial Pipeline, and Oldsmar Water, and then we closed out the year with good old Log4J. With just one quarter of 2022 behind us, we are seeing threats to xIoT continuing to grow at an alarming rate. Right now, ransomware related data breaches are doubling every two years. By the end of 2022, we expect to see ransomware surpass phishing as the number one root cause of compromises.
Even with many attacks around the world, the majority of the victims so far are U.S. based / owned organizations. The victims are spread out across many industries, including construction and engineering, retail, transportation, commercial services, insurance, machinery, professional services, telecommunication, auto components, and pharmaceuticals. As further evidence of this rapidly expanding threat, a new joint draft report issued by leadership of the U.S. Department of Homeland Security (DHS) and Department of Commerce said firmware presents “a large and ever-expanding attack surface” for attackers to gain access to what is essentially the core of modern computing.
“Firmware can also be a lucrative target with a relatively low cost of attack. Over the past few years, hackers have increasingly targeted firmware to launch devastating attacks.” The 96-page report (PDF), published to support the Biden Executive Order on securing America’s supply chains, warned that firmware’s privileged position in the computing stack gives stealthy attackers a major advantage.
[ARTICLE: Microsoft: Firmware Attacks Outpacing Security Investments]
Despite its essential role in electronic devices, the agencies noted in the report insist that firmware security “has not traditionally been a high priority for manufacturers or users and is not always well protected.”
As your organization moves to adopt more and more XIoT devices and technologies, it's important to manage the associated risks. By definition, XIoT encompasses a vast array of devices and systems ranging from network devices, to cameras, cars, and satellites; basically anything that requires firmware to enable its functionality. Of course once connected to a network, each of these important and useful devices comes with its own set of potential risks. One of the major security challenges is that the manufacturers of these devices are frequently not aware of vulnerabilities in the components that make up their firmware. Many components are part of open source shared libraries and operating systems such as Embedded Linux. Therefore, asking a manufacturer that has hundreds of different devices on the market (or even just a few), “Does your code contain the latest exploit that is in the news today?” (e.g. Log4J) can be an effort in futility.
As a result, it is important that Security and Risk Management teams identify the risks in the devices they use, and develop practical plans of mitigation where possible, and risk acceptance where mitigation is not possible. The strategy is identifying the ghost(s) in the machine. The number one focus should be protecting your organization's data and infrastructure. The NetRise Turbine platform can give you the kind of insight into these XIoT devices that previously required highly skilled reverse engineers and pen testers to achieve. We do this with a simple but powerful SaaS platform that helps you determine which risks to address first, and which should be monitored until fixed by the manufacturer or open source community.
At NetRise, our number one goal is to provide XIoT visibility to device vulnerabilities and risk, and help organizations that increasingly rely on these devices in a connected world to stay safe!
For more information or support with XIoT security, please reach out to us today.
Stay up to date with the news
Sign Up To Get Our Free Insights Delivered To Your Inbox
You might also like
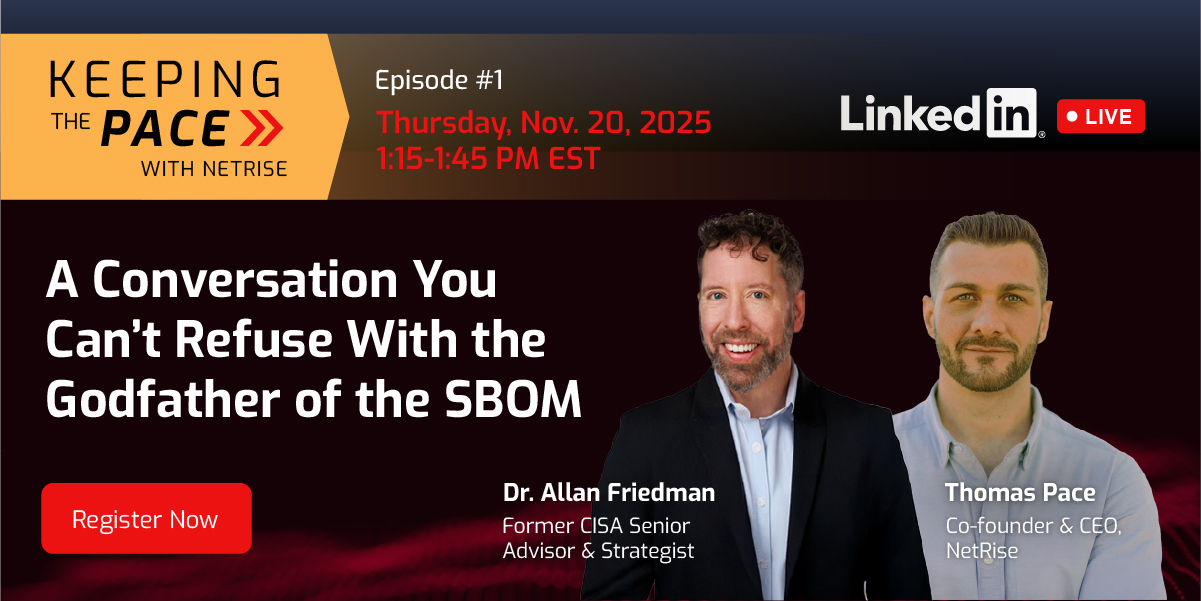
Explore other exciting events!