Manufacturers must ensure that software and devices are released without known exploitable vulnerabilities and that security issues are addressed before products reach customers.
EU Cyber Resilience Act Data Sheet
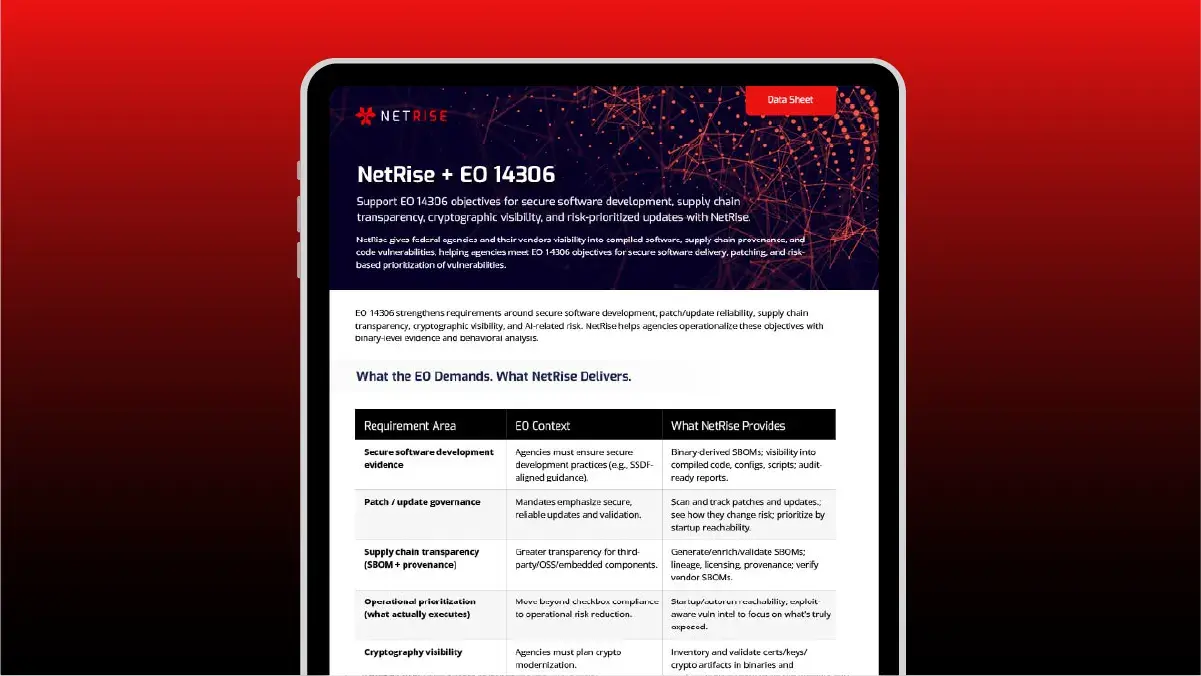
Meet EU Cyber Resilience Act (CRA) requirements with compiled-code analysis, SBOM validation, and audit-ready evidence aligned to regulator expectations.
EU Cyber Resilience Act Data Sheet
Meet EU CRA obligations with binary-derived SBOMs, vulnerability evidence, and audit-ready reporting.

Why This Data Sheet Matters:
This data sheet shows how those requirements translate into operational reality.
The CRA raises the bar for software security and accountability. Compliance now requires verifiable technical evidence, not policies or questionnaires.
Organizations must be able to demonstrate that:
Organizations must be able to produce accurate SBOMs that represent the actual compiled components running in software and devices.
Organizations must maintain clear technical documentation and evidence demonstrating compliance with CRA requirements during audits or regulatory review.
What You’ll Learn:
CRA requirements
Expectations
Documentation
Prioritization
Audit-readiness
Operationalizing Cyber Resilience Act Readiness
- Secure-by-Design & Secure-by-Default Evidence
- Vulnerability Handling & Patch Governance
- Supply Chain Transparency & SBOM Validation
- Operational Prioritization (What Actually Executes)
- Cryptography Visibility & Key Management
- Reporting, Disclosure & ENISA Alignment
NetRise analyzes the final compiled software that ships and runs, enabling organizations to produce defensible CRA evidence tied to real execution.
With NetRise, teams can:
- Generate and validate binary-derived SBOMs (SPDX, CycloneDX)
- Identify vulnerabilities in startup-loaded components
- Validate kernel vulnerabilities and fixes with KVAR workflows
- Detect misconfigurations, embedded secrets, and crypto risk
- Produce CRA-aligned reports for audits, CE marking, and ENISA reporting
- Maintain version history and traceability across releases
How NetRise Supports CRA Readiness:
Binary-Derived SBOM Generation & Validation
Startup Component Vulnerability Detection
Identify vulnerabilities in startup-loaded components
Kernel Vulnerability Validation (KVAR)
Validate kernel vulnerabilities and fixes with KVAR workflows
Embedded Risk & Misconfiguration Detection
Detect misconfigurations, embedded secrets, and crypto risk
CRA-Aligned Compliance Reporting
Produce CRA-aligned reports for audits, CE marking, and ENISA reporting
Release Traceability & Version History
Maintain version history and traceability across releases
Who This Data Sheet Is For:
Product Security & Engineering Teams
Security and engineering teams responsible for identifying vulnerabilities, validating software components, and improving the security posture of their products.
GRC, Compliance & Regulatory Leaders
Software & Device Manufacturers selling into the EU
Third-Party Risk & Procurement Teams
Security Leaders preparing for CRA enforcement
Download the EU Cyber Resilience Act (CRA) Compliance Data Sheet
Get a practical breakdown of what the EU CRA requires — and how organizations can meet those obligations with defensible, audit-ready evidence. Learn how binary-derived SBOMs, execution-aware vulnerability analysis, and continuous software visibility help manufacturers and buyers demonstrate compliance, reduce regulatory risk, and prepare for CRA enforcement with confidence.
You might also like
Learn how we helped the customers to reach the next level