Quantum Computing Will Be Here Before You Know It. Identify and Strengthen Encryption of Your Assets Now
NetRise now identifies algorithms that protect your encrypted assets to assess your risk and help you prepare for Post-Quantum Compliance.
Post-Quantum Cryptography (PQC) risk is simple: cryptography that protects sensitive data today won’t protect it forever. Quantum computing is expected to have the power to break widely used encryption algorithms, which is why attackers can “harvest now, decrypt later” (HNDL) - collecting encrypted data now with the intent to decrypt it as soon as they’re able. That’s why PQC readiness starts with knowing where quantum-vulnerable cryptography exists across the systems you rely on.
The hard part of PQC readiness is answering the question most organizations can’t answer with confidence:
Where, exactly, is quantum-vulnerable cryptography embedded across the software assets we deploy and depend on?
That question matters now because OMB M-23-02 directs federal agencies to submit an annual, prioritized inventory of cryptographic systems vulnerable to cryptographically relevant quantum computers (CRQCs), and CNSA 2.0 sets a 2027 horizon for quantum-safe requirements in new National Security System (NSS) acquisitions. Gartner analysts project conventional asymmetric cryptography may be unsafe by 2030 - so organizations with long-retention data can’t afford to treat PQC as a distant future initiative.
Even outside these timelines, HNDL risk makes PQC planning urgent anywhere long-lived sensitive data is involved—especially in financial services and healthcare delivery organizations handling PII and protected health information.
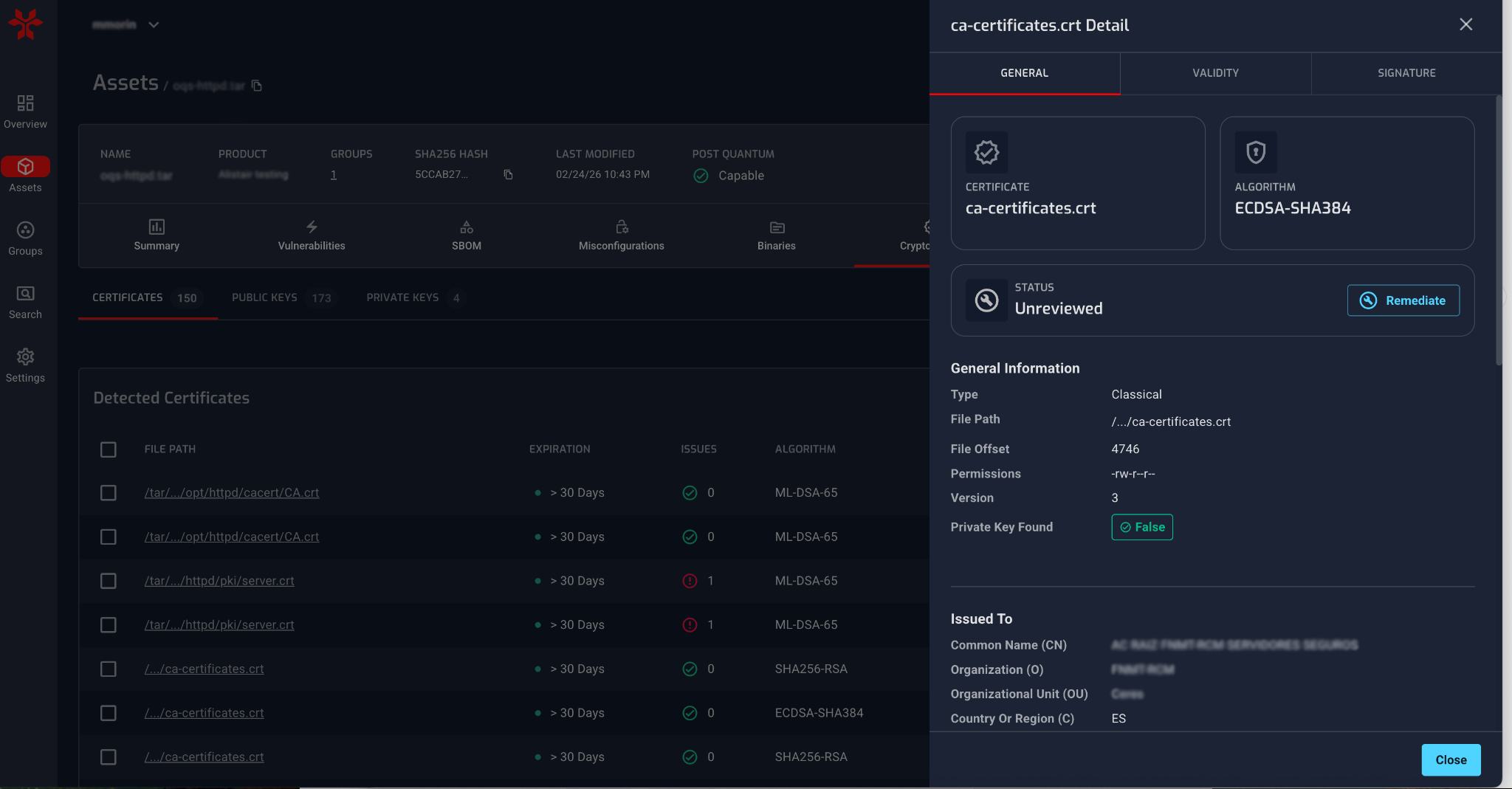
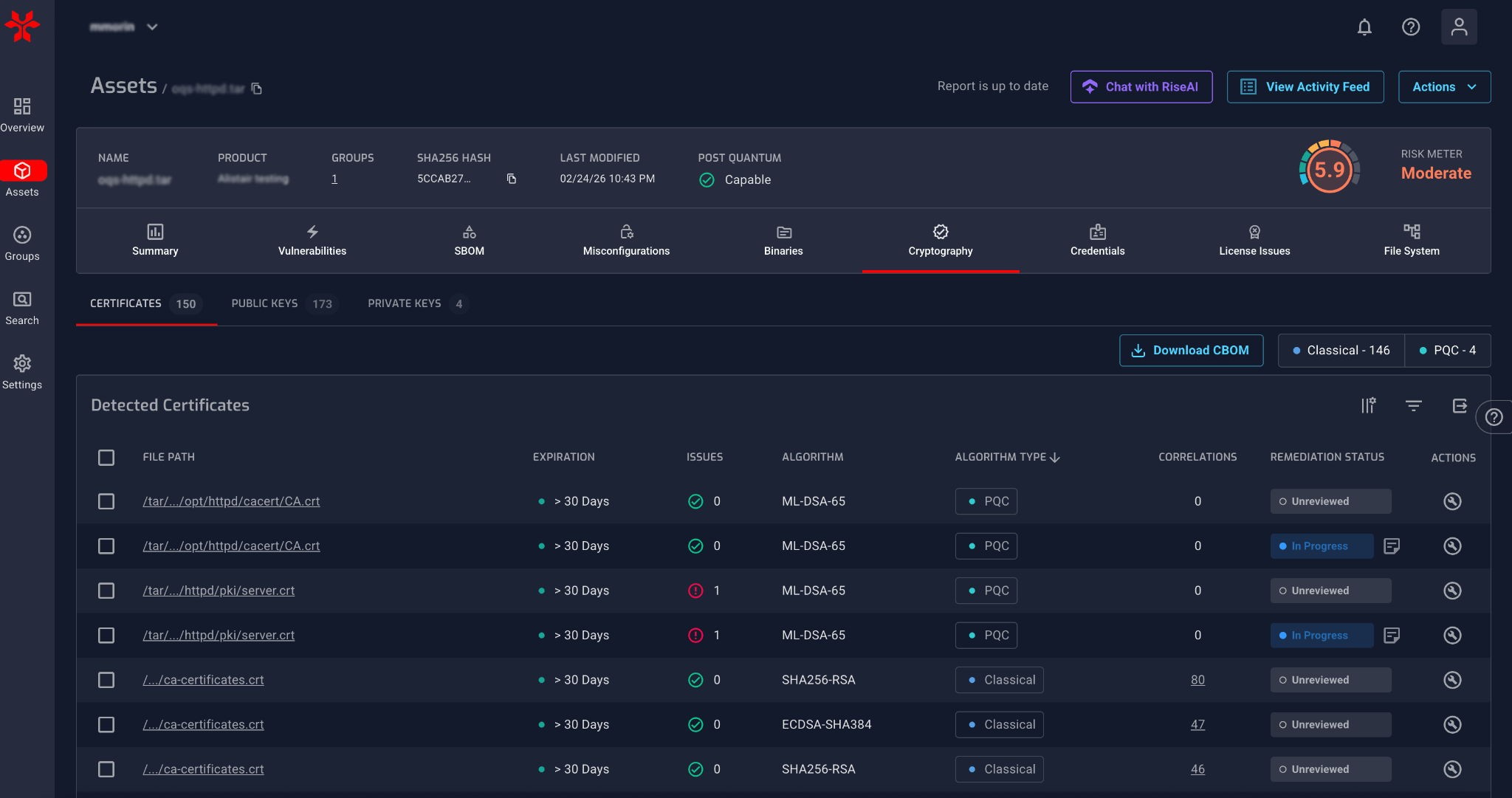
That’s why we’re expanding NetRise cryptographic analysis capabilities to help teams discover, classify, and report cryptography across real-world artifacts - including firmware, operating systems and kernels, executables, containers, and compiled libraries. This helps teams evaluate what’s actually deployed—not just what’s declared in source repositories.
The problem with PQC readiness: You can’t fix what you can’t see
PQC readiness breaks down when teams don’t know where they’re starting: what cryptographic assets exist in the software they run, and which are exposed to post-quantum risk. You can’t prioritize what to modernize until you can see the algorithms, certificates, and keys you’re actually running.
The challenge is that many of the signals that matter—expired certificates, weak or exposed keys, and legacy algorithms—live inside compiled artifacts in production. If you’re only looking at documentation, declarations, or source-level intent, you can miss what’s actually shipped.
Even when an expired certificate isn’t actively used, its presence often signals stale cryptographic assets still being shipped. Cleaning up unused or outdated certificates and keys can reduce attack surface—and it’s frequently the first “easy win” teams uncover once they can see what’s inside their deployed artifacts. Just as important, finding outdated certificates is often a sign that no one has been looking for them in the first place—which raises a bigger question: if these were missed, what else might be embedded in the artifact and going unnoticed?
You need a way to see cryptography across operational systems and vendor releases and updates, then prioritize what to modernize based on data shelf-life and system longevity—a common pressure point for federal programs and highly regulated sectors like financial services and healthcare.
That’s why comprehensive cryptographic visibility across deployed artifacts becomes the foundation for PQC planning, remediation tracking, and readiness reporting.
Get ready for PQC with NetRise
In practice, teams need to separate cryptography that is likely to remain safe in a post-quantum world from cryptography that will need to be replaced—then prioritize by data shelf-life and system longevity.
Instead of treating PQC as a future checkbox, the goal is to help teams do three practical things right now:
1) Identify PQC-ready vs quantum-vulnerable crypto faster
NetRise adds clearer classification so teams can distinguish classical (quantum-vulnerable) and PQC (quantum-resistant) cryptography across certificates, public keys, and private keys so you can flag systems in scope for CNSA 2.0 transitions and prioritize those that protect high-value data or have long service lives.
We also flag quantum-capable assets—assets with software capable of supporting PQC algorithms. This helps your teams prioritize where PQC adoption may be feasible sooner, while recognizing runtime configuration determines what’s actually used.
2) Turn cryptographic inventory into a PQC readiness plan
PQC readiness is fundamentally an inventory and planning problem: locate and classify quantum-vulnerable algorithms within software components, understand where they are used in live systems, and validate what vendors tell you in your third-party risk programs.
NetRise supports that modernization workflow by:
- Linking findings to the assets they came from, tracking remediation status, and preserving analyst notes, so you can decide what belongs on PQC roadmaps, Plans of Action and Milestones (POA&Ms), and program plans.
- Providing deeper certificate visibility by flagging common issues—like expired or soon-to-expire certificates, weak or exposed keys, and legacy algorithms—so teams can review and prioritize remediation - or removal - faster.
- Supporting an interactive remediation workflow so teams can track status, record decisions and notes, and build an operational record that can be reused across reporting cycles.
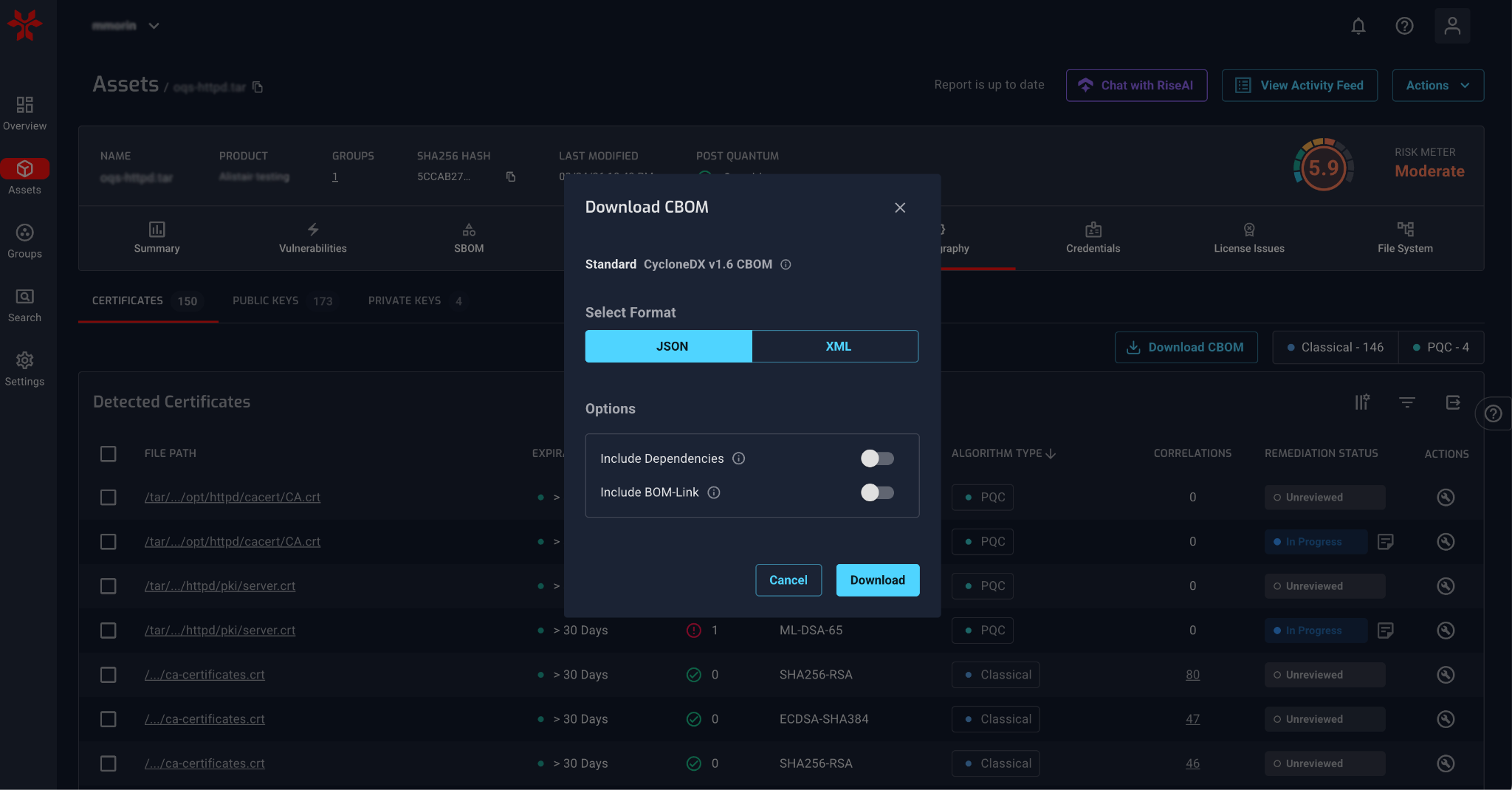
3) Produce audit- and exec-ready reporting to track and report on PQC readiness
PQC readiness has to be measured, reported, and revisited. To support that, NetRise provides reporting outputs that you can use directly in formal processes:
- A PQC readiness PDF report designed for executives, program offices, and oversight bodies, with KPI-style summaries, algorithm distributions, and remediation status across systems
- A CBOM export, aligned to CycloneDX 1.6, that provides a machine-readable inventory of cryptographic elements (including algorithm identifiers, key sizes, and technical hashes) so teams can integrate crypto inventory into downstream systems, standardize documentation, and support repeatable readiness workflows
The goal is to replace one-off spreadsheet reconstruction with repeatable reports that contracting teams, auditors, and program managers can read and act on.
How this fits into PQC readiness workflows
NetRise PQC capabilities are built for the teams who actually have to execute post-quantum transitions:
-
Federal agencies and program offices that need fleet-wide cryptographic inventories, prioritized PQC plans, and reporting they can stand behind.
-
System integrators and OEMs that must demonstrate PQC readiness to stay eligible for high-value government and enterprise contracts.
-
Highly regulated enterprises (financial services and healthcare delivery organizations) that need to reduce HNDL exposure for PII/PHI and other long-retention data.
With NetRise, you’ll get the visibility, prioritization, and reporting you need to plan and execute a PQC migration program with confidence.
PQC readiness begins with what you can verify
Post-quantum readiness starts with understanding your cryptographic footprint across the binaries you ship and the software you deploy. NetRise helps you uncover that footprint so you can plan, prioritize, and work toward PQC readiness.
Want to see what PQC readiness looks like in your environment? Explore NetRise PQC Readiness Reporting and schedule a demo.
Frequently Asked Questions
What is post-quantum cryptography (PQC) risk and why does it matter now?
Why is identifying quantum-vulnerable cryptography in deployed software so difficult?
How does NetRise help organizations prepare for post-quantum cryptography readiness?
NetRise helps organizations prepare for PQC readiness by providing visibility into cryptographic assets across deployed software, including firmware, operating systems, containers, and binaries. It identifies and classifies cryptographic algorithms, certificates, and keys to distinguish quantum-vulnerable from quantum-resistant elements. NetRise also supports prioritization by linking findings to assets, tracking remediation, and generating reports such as PQC readiness summaries and CBOM exports. This allows teams to build actionable migration plans, support compliance requirements, and track progress over time.
Stay up to date with the news
Sign Up To Get Our Free Insights Delivered To Your Inbox
Recent Press Releases
Stay up to date with the latest official announcements and corporate milestones from NetRise.